Introduction
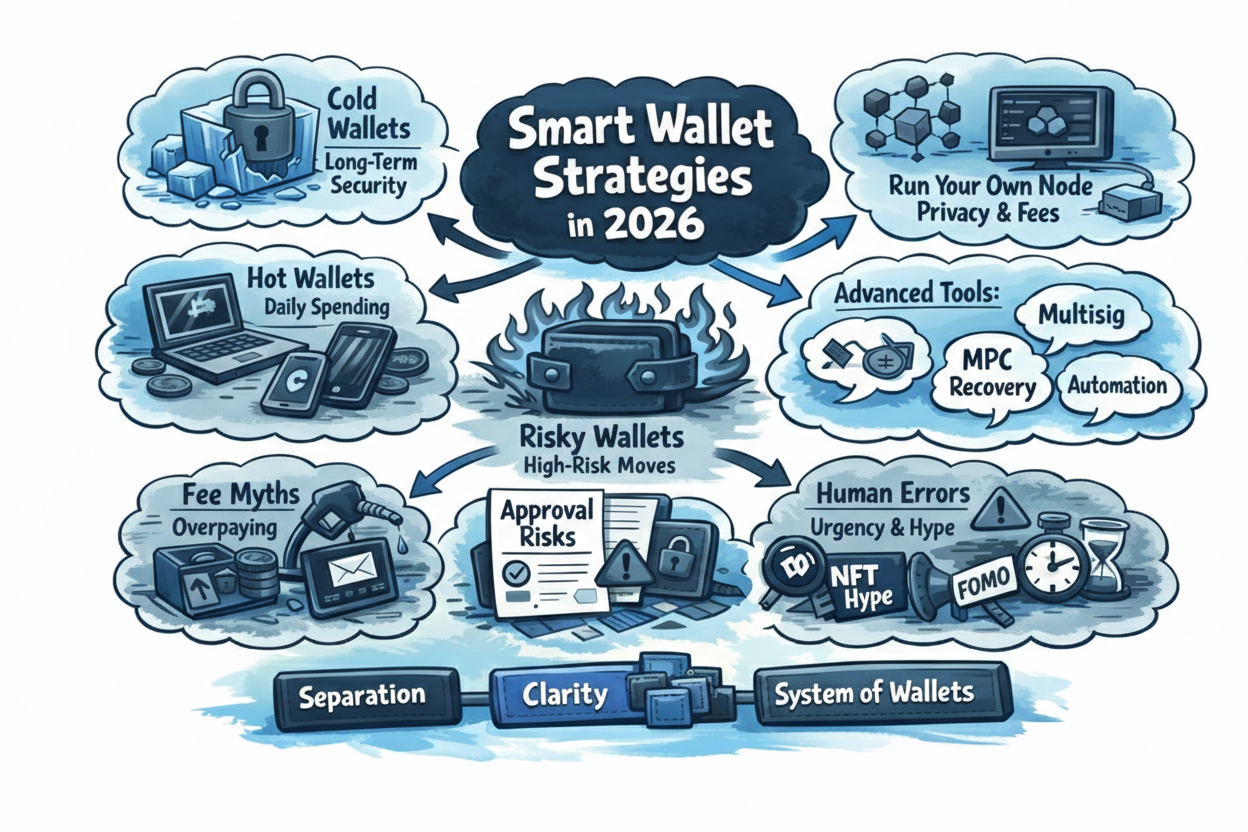
By 2026, cryptocurrency wallets are no longer simple storage tools. They are complex systems, bridging multiple blockchains, integrating staking, NFTs, DeFi, and user authentication, while simultaneously acting as the primary interface between users and digital assets. Despite advances in cryptography, signature schemes, and hardware isolation, millions of users continue to lose funds each year, not because of weak encryption, but because wallet design and operational practices fail to account for real-world human behavior.
The core challenge is complexity disguised as simplicity. Wallets promise “non-custodial security,” “one-click swaps,” or “automatic gas fees,” yet these conveniences often hide critical decisions. Users may approve unlimited token allowances, transact on the wrong chain, or trust a swap aggregator without realizing custody has shifted temporarily to a centralized API. Each of these small missteps compounds risk in a system where errors are irreversible.
This article examines the state of wallets in 2026, focusing on the following pillars:
- Types of wallets and their architecture — how design choices affect control, privacy, and risk.
- UX and human factors — why poor interface design is the leading cause of fund loss.
- Real-world hacks — lessons drawn from high-profile incidents across Bitcoin, Ethereum, Solana, and multi-chain wallets.
- Strategic wallet architecture — operational models that reduce risk without sacrificing usability.
- Advanced security features and recommendations — from multisig and MPC to recovery practices and supply chain verification.
By integrating these pillars, this guide provides a comprehensive, operationally focused view of wallet security. It goes beyond generic advice, showing what works, what fails, and why, based on observable case studies and best practices.
A key insight underpins the entire analysis: security is not a single feature, it is a system. No wallet, hardware, or cryptographic protocol alone can prevent loss. Instead, resilience comes from layered custody, operational discipline, clear interfaces, and informed decision-making. Understanding this principle is essential for anyone holding cryptocurrency in 2026, from hobbyist traders to enterprise treasury managers.
Finally, the article emphasizes realistic trade-offs. There is no universal “best wallet.” Some tools maximize usability at the cost of privacy or fee control. Others prioritize absolute control, sacrificing convenience. The goal is to help users understand these trade-offs, match wallet architecture to their operational needs, and adopt behaviors that minimize catastrophic loss.
In parallel, the market narrative around the best crypto wallets has shifted from pure self-custody toward multi-functional financial platforms. Modern wallets now compete not only on strong security, but also on user-friendly interfaces, mobile app performance, and broad compatibility across ecosystems. A wallet in 2026 is expected to support Bitcoin, EVM networks, Solana, Layer 2 solutions, NFTs, and multiple forms of stablecoins, while also offering on-ramps to fiat payment systems.
However, expanded functionality increases systemic exposure. Cross-chain bridges, embedded swap aggregators, and in-app staking modules introduce new trust assumptions. What appears seamless in a mobile interface may rely on centralized relayers, external liquidity providers, or partially custodial infrastructure. These layers often operate outside the user’s visibility, yet they materially affect risk.
The rise of stablecoins as transactional infrastructure further reshapes wallet usage patterns. Many users now treat wallets as daily payment tools rather than cold storage devices. This shift elevates the importance of real-time monitoring, gas optimization, and transaction clarity—particularly within the EVM environment, where fee mechanics and approval models can create hidden liabilities.
At the same time, scams have evolved alongside wallet sophistication. Phishing interfaces increasingly mimic legitimate wallet popups. Malicious dApps exploit unlimited token approvals. Fake bridge confirmations and counterfeit support chats target users directly inside otherwise legitimate applications. Even the most secure wallet architecture cannot fully prevent losses if interface design fails to clearly distinguish between transaction signing, token approval, and delegated authority.
As a result, evaluating the “best” wallet in 2026 requires more than comparing feature lists. It requires analyzing architectural transparency, fee logic, approval management, cross-chain execution models, and how clearly the wallet communicates risk at the moment of signature. Security today is not just cryptographic strength — it is how effectively the wallet reduces ambiguity at critical decision points.
This broader perspective frames the deeper analysis that follows.
With this framework in mind, we now move into Part 2 — Types of Wallets and Their Architecture, exploring the foundational choices that define user control, privacy, and security.
Wallet Types and Architecture
By 2026, the choice of a cryptocurrency wallet directly affects security, control, and operational convenience. Every wallet type comes with trade-offs: greater control often means more responsibility, while higher usability often hides risks. Understanding these trade-offs is critical for users managing significant digital assets.
Native Bitcoin Wallets
Native Bitcoin wallets like Electrum, Wasabi, and Sparrow remain the gold standard for transparency and control. They allow users to manage fees, UTXOs, support Replace-by-Fee (RBF), Child-Pays-for-Parent (CPFP), and provide privacy-enhancing features such as CoinJoin.
Example: An Electrum user sending 0.5 BTC can manually set the fee to 50 sat/byte, while Sparrow supports RBF to accelerate a transaction if the network is congested. Wasabi, emphasizing privacy through CoinJoin, restricts fine-grained fee adjustment but provides advanced anonymity features.
Comparative Table: Native Bitcoin Wallets
| Wallet | Fee Control | Privacy | Multisig | Hot Wallet UX |
| Electrum | Full, RBF/CPFP | Minimal | Yes | Medium |
| Wasabi | Limited | CoinJoin | Yes | Medium |
| Sparrow | Full | Optional | Yes | Medium |
Key considerations:
- Full Node vs RPC: Advanced users run their own Bitcoin node for privacy and precise fee estimation, but this is unnecessary for small payments.
- Trade-offs: Full control means responsibility for seed phrase management, recovery, and software updates.
Fee mechanics
Fee control allows:
- manual sat/vB input
- Replace-By-Fee (RBF)
- Child-Pays-For-Parent (CPFP)
- full coin control
This matters during congestion. Instead of overpaying, users can:
- send with a low fee
- wait
- bump only if needed
This alone often saves more than any “discounted transaction fees” offered by platforms.
Node requirement
- Own node: optional but recommended
- Without a node, privacy depends on server trust
- With a node, wallet becomes close to full self-custody
CoinJoin explained simply
CoinJoin mixes multiple users’ UTXOs into a single transaction so that:
- input-output links are blurred
- blockchain analysis becomes probabilistic, not deterministic
This does not make transactions invisible, but it raises the cost of surveillance.
Fees and hidden costs
CoinJoin introduces:
- coordinator fees
- mining fees
- time cost
Node usage
- Own node: optional
- Without own node, metadata leakage still possible
- With node, privacy improves significantly
Controversies & risks
- Some CoinJoin outputs have been flagged by exchanges
- Not a technical flaw, but a compliance reaction
Why adjustable fees actually reduce risk
Most people think lowering fees increases risk. In reality, fixed fees increase risk.
Here’s why:
- Wallets with static fee logic guess future mempool conditions
- If congestion spikes, transactions stall
- Users panic and resend, often duplicating fees
Wallets that allow fee modification let users:
- react to real conditions
- avoid overpayment
- keep capital liquid
This is especially relevant for bitcoin payments used in commerce or treasury management.
Multi-Chain and Web3 Wallets
Multi-chain wallets consolidate multiple blockchains (Ethereum, Polygon, Solana, etc.) into a single interface (e.g., MetaMask, Phantom, Rainbow). They offer convenience but add hidden complexity: fee abstraction, swap routing through centralized liquidity providers, and approvals that remain invisible after signing.
Example: A MetaMask user sees “Swap ETH → USDC” and assumes it is fully non-custodial. In reality, the transaction may route through an aggregator with centralized liquidity and be subject to AML filtering, potentially delaying or freezing the funds.
Why multi-chain wallets exist at all
Native wallets optimize for one chain. Multi-chain wallets optimize for interaction.
They are built for:
- DeFi
- NFTs
- staking
- browser-based dApps
- rapid on-chain experimentation
This makes them ideal for:
- beginners
- users moving between ethereum, solana, polygon, and other networks
- people who value speed over protocol purity
But it also introduces new failure modes.
MetaMask — the default Ethereum gateway
MetaMask is not just a wallet. It is middleware between users and web3.
Architecture
- Ethereum-first
- EVM-compatible chains (Polygon, BSC, Arbitrum, etc.)
- Browser extension + mobile app
- Relies on RPC providers (Infura by default)
What MetaMask abstracts away
- gas estimation
- nonce handling
- contract call complexity
This abstraction improves usability, but hides:
- exact contract behavior
- downstream approvals
- long-term permissions
Fee control
- Adjustable gas price and gas limit
- Users can lower fees, but:
- bad estimates can cause failed transactions
- failed transactions still burn gas
Common hack pattern
Approval drain attacks
Users approve unlimited token spending to a malicious contract. Later, the contract drains funds without another signature.
Why this works
- UI shows “Approve token”
- Not “Grant infinite spending rights forever”
Most losses attributed to “wallet hacks” are actually permission abuse.
Phantom — Solana UX done right
Phantom became popular because it did something rare: it made Solana feel approachable.
Architecture
- Solana-native
- Browser extension + mobile
- Tight integration with NFT marketplaces
UX strengths
- Clear transaction previews
- Human-readable messages
- Simple staking flow
Trade-offs
- Less granular fee control
- Relies on Solana RPC infrastructure
- Less suitable for long-term cold storage
Hack reality
Solana wallet compromises usually happen via:
- fake NFT mints
- malicious signing requests
- clipboard address replacement malware
Not protocol failures — social engineering.
Trust Wallet — mobile-first, broad coverage
Trust Wallet aims to be “everything in one app.”
Architecture
- Multi chain support (BTC, ETH, SOL, TRX, etc.)
- Mobile app (iOS / Android)
- Integrated DEX and staking
Strengths
- Simple onboarding
- Good for stablecoins
- Built-in staking for some networks
Weaknesses
- Limited transaction introspection
- Less visibility into contract logic
- Heavy reliance on UI trust
This is a classic trade: high usability → reduced transparency
Rabby Wallet — power-user response to MetaMask
Rabby was built to fix MetaMask’s biggest weakness: blind signing.
What Rabby does differently
- Simulates transactions before signing
- Shows token balance changes
- Warns about suspicious approvals
Why this matters
Many web3 exploits rely on:
- users not understanding what they sign
- contracts behaving differently than expected
Rabby reduces this risk, but:
- still depends on RPC data
- still vulnerable to novel contract logic
Browser extensions: the largest attack surface
Browser extension wallets are convenient — and dangerous.
Attack vectors
- malicious extensions
- compromised updates
- injected scripts
- clipboard hijacking
This is why many advanced users:
- interact via browser wallets
- but store funds in hardware wallets
NFT support: convenience vs clarity
NFT wallets prioritize:
- visual galleries
- floor prices
- marketplace integration
But NFTs introduce risks:
- fake collections
- malicious metadata
- phishing via “airdrops”
Wallets rarely verify:
- contract legitimacy
- creator authenticity
Which means UI ≠ safety.
Staking inside wallets — hidden complexity
In-wallet staking looks simple:
“Stake → earn → withdraw”
What’s hidden:
- lock-up periods
- slashing risk
- validator trust
Some wallets take:
- protocol fees
- routing fees
- validator commissions
Often without clear disclosure.
Comparison table — major multi-chain wallets
| Wallet | Chains | NFT Support | Staking | Fee Control | Risk Profile |
| MetaMask | EVM | ⚠️ basic | ❌ | ⚠️ partial | High (approvals) |
| Phantom | Solana | ✅ strong | ✅ | ❌ limited | Medium |
| Trust Wallet | Multi | ✅ | ✅ | ❌ limited | Medium |
| Rabby | EVM | ⚠️ | ❌ | ⚠️ partial | Lower |
| Coinbase Wallet | Multi | ⚠️ | ⚠️ | ❌ | Medium |
Hardware Wallets and Cold Storage
Hardware wallets like Ledger, Trezor, and Coldcard remain the standard for long-term storage. Their goal is minimizing online exposure, but they cannot protect against supply chain attacks or human errors, such as entering a seed phrase into a compromised device.
Example: A Trezor user stores 10 BTC in cold storage, connecting the device only monthly to sign a transaction. No browser extensions, NFTs, or approvals are used. If the device firmware or supply chain is compromised, the funds are lost entirely.
Comparative Table: Hardware Wallets
| Wallet | Fee Control | Multi-Chain | Hot Wallet UX | Supply Chain Risk |
| Ledger | Software-dependent | Limited | Medium | Medium |
| Trezor | Software-dependent | Limited | Medium | Medium |
| Coldcard | PSBT-enabled | Bitcoin only | Minimal | Low |
Key considerations:
- Cold storage ≠ protection from human error. Mistakes during seed recovery or a compromised PC can fully compromise funds.
- MPC and multisig add convenience and distribute risk but require coordination and trust, reducing absolute self-sovereignty.
What a hardware wallet really is (and is not)
A hardware wallet is not a magic safe. It is a key isolation device.
Its core purpose:
- private keys never leave the device
- signing happens inside secure hardware
- malware on your computer cannot directly steal keys
What it does not do:
- verify that a transaction is “good”
- protect you from signing malicious data
- guarantee recovery if you lose backups
Security depends on:
- firmware integrity
- display verification
- user behavior
Trezor vs Ledger — two philosophies
Trezor
- Fully open-source firmware and hardware design
- No secure element (by design choice)
- Relies on transparency and audits
Implication:
Anyone can inspect the code. Physical access attacks are theoretically easier, but software trust is higher.
Ledger
- Closed-source secure element
- Proprietary firmware components
- Physical attack resistance prioritized
Implication:
Better against physical theft, weaker transparency guarantees. This is not “good vs bad” — it is threat-model dependent.
Firmware risk: the most ignored attack vector
Most users trust firmware blindly.
Reality:
- firmware updates can introduce bugs
- supply-chain compromises are real
- malicious updates bypass user expectations
Historical examples:
- wallet firmware bugs enabling memory leaks
- compromised build pipelines (industry-wide problem, not wallet-specific)
Mitigation
- verify firmware signatures
- delay updates
- follow independent audits, not marketing claims
Display verification: the real security boundary
A hardware wallet is only as safe as: what its screen shows vs what you approve.
If your computer shows: “Send 0.01 ETH” but the device shows: “Contract call: approve unlimited spending” and you approve anyway — the device worked correctly.
The user failed, not the hardware.
This is why:
- small screens are a real usability risk
- long hex data increases blind signing
- smart contract UX matters more than key storage
Cold storage ≠ air-gapped ≠ secure by default
Let’s define terms precisely.
Cold storage
- keys not on an internet-connected device
Air-gapped
- no physical or wireless connection during signing
Secure
- depends on operational discipline
Examples of insecure “cold” setups:
- Seed phrase typed into a compromised PC
Imagine a very common situation.
Someone buys a hardware wallet and follows most of the “best practices,” but during setup decides to type the seed phrase on a computer because it feels more convenient.
What actually happens:
- the PC may already be infected with malware, a keylogger, or a malicious browser extension;
- the seed phrase is transmitted to an attacker the moment it is typed;
- the wallet itself remains offline and safely stored…
but the funds are already compromised.
Key point:
it does not matter that the wallet is a hardware device — if the seed phrase ever touches an online device, cold storage no longer exists.
- QR signing via a malicious camera app
Another common scenario involves “secure” QR-based transaction signing.
How it usually looks:
- the user relies on an offline device or hardware wallet;
- QR codes are scanned using a smartphone camera;
- the phone runs a third-party or modified camera application.
The real risk:
- the app may store or upload scanned QR images;
- QR codes may contain more than just a transaction request;
- in certain cases, attackers can reconstruct transaction details or address activity.
Result: The private key is not directly stolen, but transaction privacy and security are silently compromised, often without any visible warning.
- Backups photographed on a phone
One of the most frequent and underestimated mistakes. “I’ll just take a photo of the seed phrase and delete it later.”
What usually goes wrong:
- the image is automatically synced to iCloud or Google Photos;
- backups propagate across multiple devices;
- a cloud account is later compromised through phishing or credential leaks;
- the seed phrase becomes accessible months or even years later.
The irony:
- a phone feels personal and safe;
- in reality, it is the most frequently attacked device most people own.
Cold storage reduces remote attacks, not human error.
Takeaway:
Wallet choice depends on the user’s goals. Long-term storage prioritizes isolation and minimal online exposure, while frequent DeFi or NFT interactions favor multi-chain convenience. Each option comes with trade-offs: higher control increases responsibility, and higher convenience increases hidden risks.
UX and Human Factors in Security
By 2026, most wallet losses are not caused by cryptography failures but by interface design and human behavior. Even with mature signature schemes, hardware isolation, and audited software, poor UX still leads to millions in lost funds each year. Understanding how users interact with wallets is crucial for mitigating these losses.
Confirmations, Approvals, and Invisible Risk
The simplest “Confirm” button can hide catastrophic risks. In many wallets, a user sees a token logo, an amount, and a network fee, but the UI rarely communicates what is actually being signed. Is it a token transfer, an approval, or a swap? Does the approval last indefinitely?
Example: An Ethereum user approves an ERC-20 token in MetaMask, trusting the default “unlimited approval” option. Weeks later, a compromised DApp drains the wallet. The wallet never technically failed, but its interface concealed critical information at the moment of consent.
Approvals are silent liabilities: they outlive the wallet balance, the original transaction context, and often even the user’s memory. Advanced users mitigate this by reviewing approvals weekly and separating approval interactions into dedicated wallets. Beginners typically accept defaults, creating a persistent attack surface.
Gas Fees, Mempools, and Misleading Abstraction
Wallets increasingly abstract gas and fees to simplify user experience. While this reduces friction, it removes user agency. Users rarely understand why fees spike or whether their transaction is actually prioritized.
Example: A Solana user on a low-fee chain sees “near-zero fees” and assumes instant confirmation. In reality, a congested mempool or poor routing can delay the transaction for hours. Advanced wallets like Electrum or Sparrow show mempool state and allow manual fee adjustments, preventing overpayment or stuck transactions. Multi-chain wallets often hide these controls, masking risk rather than eliminating it.
Key lesson: Paying more does not guarantee faster confirmation. Understanding fee markets is critical, especially for active traders and DeFi users.
Browser Extensions and Persistent Exposure
Browser-based wallets continue to be a major attack vector. Extensions often inherit the trust of the browser environment, meaning malicious sites can inject code or modify transactions without explicit user awareness.
Example: A user interacts with an NFT minting site using MetaMask. A malicious Chrome extension injects a fake signing request. The wallet UI appears legitimate, but the transaction is altered to send funds to an attacker. Because extensions are persistent and session visibility is weak, the user may remain unaware of exposure until significant losses occur.
Recovery UX and False Security
Many wallets reassure users with statements like “You can always recover your funds with your recovery phrase.” While technically true, this messaging can be misleading. Users often store seed phrases on cloud drives, take screenshots, or input them into unsafe devices under stress.
Example: A beginner user loses a hardware wallet and attempts recovery using a mobile device infected with malware. The recovery phrase is compromised, resulting in immediate theft. Wallets that simulate recovery, educate on offline backups, and enforce physical copy storage significantly reduce such risks.
UX Design Patterns That Cause Losses
- Swap Buttons: Users assume non-custodial execution, but transactions often route through centralized liquidity providers. Delays, freezes, or AML checks are hidden.
- NFT Interfaces: Thumbnails and galleries dominate UX, hiding mint contract permissions and operator approvals. Users unknowingly grant control to third parties.
- Excessive Warnings: Pop-ups for gas spikes, risky approvals, or unknown contracts often become noise. Without specificity, users habituate and click through.
- Chain Ambiguity: Multi-chain wallets hide network context, leading to “stuck” or inaccessible funds on the wrong chain.
Key takeaway: UX failures compound silently. They create a gap between user intention and blockchain reality, which cannot be fixed by cryptography alone.
This section emphasizes that human error is predictable: urgency, distraction, or unfamiliarity drives mistakes. Wallet design must prioritize clarity over speed. A wallet that slows the user down to explain exact actions, scope, and consequences is far safer than one that “simplifies” at the cost of transparency.
Wallet Types and Architecture
Understanding wallet types and their architectural trade-offs is critical to self-custody in 2026. Security, usability, and risk tolerance vary dramatically depending on whether a wallet is native to a single chain, supports multiple chains, or integrates hardware and cold storage.
Native Wallets: Bitcoin-Focused and Privacy-Centric
Native wallets like Electrum, Wasabi, and Sparrow focus on Bitcoin and similar single-chain assets. They typically offer full control over fees, transaction signing, and privacy tools like CoinJoin.
For instance, Electrum allows manual fee adjustment, Replace-By-Fee (RBF), and mempool visibility, giving advanced users the ability to rescue stuck transactions. Wasabi emphasizes privacy via built-in CoinJoin but limits granular fee control, which can frustrate users during network congestion. Sparrow is optimized for multisig setups, offering structured key management and clear transaction history, but onboarding is steeper for beginners.
Native wallets excel for long-term holders and high-value transactions, particularly when paired with personal nodes. Running a Bitcoin node removes reliance on third-party RPCs, improves privacy, and ensures accurate fee estimation for large or sensitive transfers. For small payments or daily use, native wallets may be overkill, and simpler software solutions suffice.
Multi-Chain and Web3 Wallets
Transitioning to multi-chain, wallets like MetaMask, Rainbow, and Phantom support Ethereum, Polygon, Solana, and multiple layer-2 networks. Convenience is their main advantage: users can store tokens, interact with DApps, and swap assets without leaving the app.
However, this usability comes at a cost. Fee control is often abstracted, and some wallets apply hidden routing or swap fees. Approval management is also weaker: multi-chain wallets frequently default to unlimited allowances, creating persistent attack surfaces. Users may mistakenly sign approvals on the wrong chain or interact with testnet contracts, leading to inaccessible funds or loss.
Despite these risks, multi-chain wallets are ideal for experimentation, daily transactions, and NFT minting, as long as users maintain segregated balances for riskier activity. Combining them with hot wallets for active use and cold storage for savings is a standard 2026 practice.
Hardware Wallets and Cold Storage
Hardware wallets, such as Ledger, Trezor, and Coldcard, remain the cornerstone of long-term security. By keeping private keys offline, they reduce exposure to remote attacks.
A typical cold storage setup involves storing the device in a secure location and only connecting it briefly for signing. This minimizes attack vectors but introduces single-point failure risk: compromised firmware, pre-initialized devices, or leaked recovery phrases can result in catastrophic loss.
Advanced hardware wallet users often combine multisig setups with cold storage to split trust across devices or locations. While multisig increases complexity, it dramatically reduces blast radius if one device or key is compromised.
Key distinctions for hardware wallets in 2026:
- Fee Control: Dependent on connected software; some interfaces limit customization.
- Node Strategy: Running your own node enhances trust but is optional for low-value transactions.
- Recovery: Seed phrases remain critical; secure offline backups are mandatory.
Hardware wallets are less suitable for frequent DeFi interactions or NFT mints, but they excel at isolating high-value assets from hot wallets used for active transactions.
Comparative Insights
Across wallet types, trade-offs are clear:
- Native wallets: Maximum sovereignty and fee control, but often single-chain and less convenient for web3.
- Multi-chain wallets: Maximum convenience and DApp access, but fees, approvals, and custody risks are abstracted.
- Hardware wallets / cold storage: Superior protection for large holdings; usability is limited, and supply-chain security is critical.
Table 2 — Key Wallet Characteristics (2026)
| Wallet Type | Chains Supported | Fee Control | Privacy | UX Complexity | Typical Use |
| Electrum / Sparrow | BTC only | High | High (CoinJoin, full node optional) | Moderate | Long-term holding, multisig, advanced BTC transactions |
| Wasabi | BTC only | Medium | Very High | Moderate | Privacy-focused BTC use, moderate technical knowledge |
| MetaMask / Rainbow | Multi-chain | Low–Medium | Medium | Low | DApps, NFTs, daily transactions, DeFi |
| Phantom | Solana | Low | Medium | Low | Solana NFTs, swaps, layer-2 activity |
| Ledger / Trezor | Multi-chain via software | Medium | High | Moderate | Long-term storage, high-value transactions, multisig setups |
| Coldcard | BTC only | High | High | High | Offline storage, air-gapped signing, privacy-focused BTC users |
This architecture overview emphasizes segmentation: in 2026, the most resilient strategy involves layering wallet types based on activity and risk tolerance, rather than relying on a single solution for all purposes. Native wallets handle high-value Bitcoin storage, multi-chain wallets facilitate active interaction, and hardware/cold wallets secure long-term holdings.
UX and Human Factor in Security
Even in 2026, the largest wallet losses are caused not by cryptography but by interface design and human error. Key derivation, signature schemes, and hardware isolation are now stable; vulnerabilities in these areas are rare. Yet wallets continue to drain user funds because the UI hides critical information exactly when users need it.
Action Ambiguity and “Confirm” Buttons
One of the most persistent failures is the green “Confirm” button. Users often see only the token logo, amount, and gas fee, without clear information on whether they are transferring, approving, or swapping tokens. Permissions may be permanent, and contracts can gain unlimited control, but the wallet interface treats these irreversible actions like simple app clicks.
A live example: a user intending to send 0.5 ETH to a friend accidentally grants unlimited approval to a malicious contract. The funds are drained silently, leaving the user puzzled because the interface gave no clear warning or visual context. This mismatch between user expectation and on-chain reality remains the root cause of many losses.
Approvals and Persistent Permissions
Approvals are another silent killer. Wallets often display a simple “Approve token” prompt without specifying limits, duration, or scope. Most users assume these approvals are temporary. In reality, they persist indefinitely, creating a window for attackers.
Advanced users mitigate this by weekly approval reviews, using separate wallets for high-risk interactions, and avoiding unlimited allowances. Without this discipline, a casual NFT mint or DeFi interaction months prior can allow a malicious actor to drain the wallet without any recent transaction being suspicious.
Gas Abstraction and Hidden Fees
Many wallets now offer “smart gas” or “auto fee” features, designed to simplify user experience. However, these abstractions often remove control without removing risk. Users cannot adjust fees manually, view mempool congestion, or understand the trade-off between speed and cost. Transactions get stuck or overpay, especially during periods of high network activity.
For example, a multi-chain wallet user attempting a Polygon swap might pay triple the necessary fee, believing the wallet’s “recommended fee” ensures fast confirmation. In reality, a slightly lower fee would have sufficed, and the user is left overpaying due to a lack of transparency in fee calculation.
NFT and Swap UX Failures
Wallets optimized for NFTs prioritize visuals, rarity, and galleries, not the technical implications of minting or approvals. A “Mint NFT” button may grant proxy permissions or secondary approvals that remain invisible to the user, effectively handing over control of other assets.
Similarly, “Swap” buttons that claim non-custodial operation often route through DEX aggregators, centralized liquidity, or AML-monitored services. Users assume permissionless execution, but delayed settlement, blocked transactions, or frozen funds can occur. The underlying problem is misleading UI abstraction, not protocol failure.
Browser Extension Risks
Browser-based wallets remain a persistent attack surface. Users forget which sites are connected or which sessions remain active. Malicious sites can exploit delayed prompts, replay attacks, or context-switching vulnerabilities. Even experienced users can fall victim because extension interfaces rarely indicate ongoing exposure.
A real-world example: an attacker injected JS via a fake Chrome extension targeting MetaMask. Users thought they were signing a legitimate transaction, but addresses were silently replaced. The wallet UI appeared normal, yet millions of dollars were drained because the interface failed to communicate session integrity.
Recovery UX and User Education
Recovery processes remain a critical vulnerability. Wallets often reassure users that “you can always recover with your recovery phrase,” encouraging risky behaviors like cloud backups, screenshots, or entering seeds into untrusted devices. Users under stress may Google recovery guides or interact with phishing support, compounding risk.
Best-practice wallets educate during setup, enforce offline backups, and simulate recovery, dramatically reducing catastrophic loss. Human error—not technology—is still the dominant risk vector.
Warnings, Alerts, and Habituation
Wallets attempt to mitigate risk with warnings for gas spikes, risky approvals, and unknown contracts, but overuse causes habituation. Generic or vague alerts become noise; users click through without understanding consequences. The real loss occurs not because security features are absent but because UX fails to make the stakes clear when it matters most.
Key Takeaways
- Most losses stem from UX-induced consent failures, not cryptographic flaws.
- Clear, context-rich interfaces that show scope, permanence, and risk before signing are the most effective security features.
- Segmentation of wallets (hot vs cold, native vs multi-chain) helps limit blast radius when human error occurs.
- Advanced users must pair education, workflow discipline, and interface awareness with technical safeguards to maintain real security.
This section demonstrates that in modern self-custody, interface clarity and human-centered design are as critical as cryptography. The strongest wallets are not those with the most features, but those that communicate risk effectively and preserve user agency.
Real-World Hack Analysis
Despite all the technological advancements by 2026, real-world hacks continue to reveal the human and systemic vulnerabilities that wallets expose. These case studies are not just horror stories—they provide clear lessons about UI failures, software supply chains, custody assumptions, and protocol trust.
Atomic Wallet Compromise (2023–2024)
Atomic Wallet, a non-custodial, multi-chain solution, experienced a massive drain of approximately $100–120 million. Users reported sudden balance losses across Bitcoin, Ethereum, USDT, and several altcoins. Blockchain analysis confirmed that the transactions were valid, with proper signatures, indicating that smart contracts were not exploited.
Investigators, including SlowMist, ZachXBT, and Chainalysis, identified the likely vector: a compromised update channel or dependency, causing users to install a malicious binary unknowingly. Once installed, the wallet requested recovery phrases, which were harvested immediately.
Lesson: Non-custodial wallets are only as safe as their software supply chain. Hardware isolation or cryptographic strength cannot prevent users from installing poisoned binaries.
Electrum Fake Server Attacks (2018–2022)
Electrum, a long-standing open-source Bitcoin wallet, faced repeated attacks via malicious servers. Attackers injected fake “update required” messages, redirecting users to phishing builds. Victims who entered their recovery phrases saw immediate drains, often losing millions cumulatively.
Older Electrum versions trusted server messages by default and lacked cryptographic verification clarity. Post-incident fixes included signed updates enforcement, server trust hardening, and warning banners.
Key Insight: Open-source does not prevent social engineering; it only facilitates recovery and analysis post-incident. UX must make verification and trust explicit to prevent such attacks.
Slope Wallet Private Key Leak (Solana, 2022)
Slope Wallet, a Solana mobile and browser-based wallet, exposed private keys in plaintext, sending them to centralized servers. Thousands of wallets were drained simultaneously, totaling around $8 million in losses. The rapid UX design of Solana encouraged frequent hot wallet use, often with large balances kept online.
Lesson: Performance and convenience often mask catastrophic key-handling flaws. Self-custody principles are meaningless if keys leave the device.
Wallet Approval Drainers (Ethereum, Polygon, BSC, 2021–2025)
Across Ethereum, Polygon, and Binance Smart Chain, billions were drained due to unrestricted token approvals. Users interacted with DApps, unknowingly granting unlimited allowances, which attackers later exploited.
Wallets typically showed only “Approve token” prompts without indicating scope or duration. Weeks or months later, contracts were exploited, and funds were drained.
Analytical takeaway: Approval UX is arguably the largest ongoing drain vector in web3. Even technically secure wallets fail when the interface does not clarify persistent permissions.
Browser Extension Hijacks
Malicious browser extensions remain a potent attack vector. By injecting JS into wallet contexts, attackers modify transactions or replace addresses without the user noticing. Users believe they interact with legitimate wallet UI, yet funds are rerouted or stolen.
Detection is difficult because extensions inherit browser trust, and wallet interfaces appear normal. This type of attack highlights that security is only as strong as the surrounding ecosystem, not just the wallet itself.
Lessons Across Case Studies
- Supply chain matters — even strong cryptography cannot protect against poisoned binaries or pre-initialized devices.
- UX clarity is critical — confusing approvals or hidden permissions consistently enable losses.
- Hot wallets are high-risk — frequent interaction, NFTs, and DeFi increase exposure. Segregation into hot, spending, and cold storage wallets limits blast radius.
- Human error amplifies risk — urgency, distraction, and interface ambiguity remain core failure points.
- Open-source and audits are necessary but insufficient — they reduce recovery time but do not prevent exploitation through phishing, social engineering, or software compromise.
In conclusion, these real-world hacks reveal that security is systemic. It is not about a single wallet being perfect, but how wallets, UI, protocols, and user practices interact. The most secure setups in 2026 balance technical safeguards, user agency, and procedural discipline, while acknowledging that human error and ecosystem trust are often the true attack vectors.
Wallet Strategies and Custody Models
By 2026, wallet security is no longer just about cryptography. The dominant threats come from interface ambiguity, approval mismanagement, and systemic misconfiguration. To mitigate these risks, advanced users structure their wallets into purpose-driven layers, balancing usability, security, and operational flexibility.
Segmentation of Wallet Roles
Wallets now serve distinct operational purposes, and combining functions increases risk. A typical setup separates three layers:
1. Cold Storage / Long-Term Wallets
Used for holding substantial crypto assets, often on hardware wallets like Ledger or Trezor, or multisig setups. Interaction is rare, typically monthly or less. Transactions are deliberate, with no browser extensions, swaps, NFTs, or smart contract approvals involved. This layer minimizes online risk, but if compromised—through tampered firmware, recovery phrase leaks, or supply-chain attacks—the losses are catastrophic.
2. Hot Transaction Wallets
Designed for day-to-day activity, including routine transfers and moderate balances, usually via software wallets on mobile or desktop. Users maintain small balances and avoid unlimited approvals. This wallet is assumed to be eventually compromised, so the focus is damage control rather than prevention.
3. Risk / Experimental Wallets
Used exclusively for high-risk operations: NFT minting, bridging, early protocol interaction, or speculative DeFi activity. Funds are transferred in only when needed, approvals are revoked frequently, and the mindset is disposable. Losses here are acceptable—this wallet layer absorbs experimental risk without affecting long-term holdings.
Segregation allows blast-radius control. Losses in one wallet do not propagate across the user’s entire portfolio, illustrating that system architecture matters more than any individual wallet’s security.
Fee Control and Transaction Management
Advanced wallet strategy leverages fee control as a tactical advantage. While most multi-chain wallets hide fee mechanics or enforce inflated “fast” presets, native Bitcoin wallets like Electrum and Sparrow allow:
- Manual fee adjustment
- Replace-By-Fee (RBF) and Child-Pays-for-Parent (CPFP) transactions
- Visibility into mempool conditions
This enables stuck transaction recovery and cost optimization, unlike many mobile or multi-chain wallets that trade control for simplicity. Ethereum and Solana users face similar challenges, where understanding base fees, tips, and priority markets directly affects cost and confirmation times.
Approval Hygiene
Unrestricted token approvals remain a silent liability. Users often forget unlimited allowances, allowing attackers to drain funds weeks or months later. Strategic users adopt:
- Weekly review of active approvals
- Separate wallets for approvals and DeFi interactions
- Revocation of unused permissions
Maintaining this discipline prevents approval drains, one of the largest ongoing vectors in DeFi loss.
Multisig, MPC, and Recovery Models
High-value wallets increasingly implement multi-signature setups for treasury management, shared custody, or large Bitcoin transactions. Multisig enhances security but increases complexity and coordination risk, making it unsuitable for modest individual holdings.
Emerging MPC (multi-party computation) and social recovery wallets reduce dependency on a single recovery phrase, improving usability while introducing trust assumptions. Users must understand these models do not replace secure operational discipline—they augment convenience, not sovereignty.
Node Strategy and Advanced Practices
Running a personal Bitcoin or Ethereum node provides tangible benefits:
- Removes RPC trust
- Improves privacy
- Enhances fee estimation accuracy
However, full nodes are task-specific. Large transactions and privacy-focused operations justify a node, whereas daily small payments or hot wallet activity typically do not. Advanced users may mix public RPC providers and personal nodes, avoiding single points of trust while maintaining operational efficiency.
Comparative Wallet Insights
Electrum offers full fee control, RBF, and CPFP, making it ideal for privacy-conscious or high-value Bitcoin users.
Wasabi provides privacy via CoinJoin but has limited fee customization, better suited for medium-term storage with moderate risk.
Sparrow is optimal for multisig setups, offering predictable signing behavior but a steeper learning curve.
Multi-chain wallets excel in convenience and fast onboarding, supporting Ethereum, Solana, Polygon, and BSC. However, they often hide swap fees, use custodial bridges, and limit fee tuning, making them better for spending and experimentation rather than secure storage.
Operational Takeaways
- Segregation beats strength: spreading funds across cold, hot, and experimental wallets reduces catastrophic risk.
- Fee control is strategic: ignoring mempool dynamics and RBF/CPFP tools leads to unnecessary overpayment.
- Approval hygiene saves millions: revocation and monitoring prevent delayed drains.
- Node usage is tactical, not obligatory: personal nodes increase autonomy and reliability for high-value or privacy-centric users.
- Advanced custody layers (multisig, MPC) improve resilience, but only if operational practices are disciplined.
This framework highlights that wallet security in 2026 is holistic: it integrates system design, transaction discipline, custody choices, and interface awareness rather than relying solely on cryptographic assurances or hardware isolation.
Advanced Security Features and Recommendations
By 2026, cryptocurrency wallets have evolved far beyond simple key storage. Security now spans device design, operational practices, transaction transparency, and advanced cryptographic techniques. This section explains what works, what introduces hidden risk, and how users can combine tools and discipline for resilient custody.
Authentication and Access Controls
Modern wallets support a range of authentication mechanisms, from PIN codes and passwords to biometric verification (fingerprint, FaceID, NFC). Hardware wallets rely on device-level authentication to isolate signing operations from malware.
Examples:
- Ledger and Trezor require PIN entry on-device for every transaction, preventing remote malware from signing without physical access.
- Mobile wallets like MetaMask Mobile or Argent combine biometric unlock with software wallets, improving usability but adding attack vectors if the phone is compromised.
Trade-offs:
Hardware authentication is strong but can be inconvenient for frequent transactions. Biometric access improves convenience but depends on the device OS’s security. Advanced users often combine hardware PINs with mobile biometrics for a layered approach.
Recovery Models: Seeds, Social Recovery, and MPC
Wallet recovery remains a critical security boundary. Traditional 12–24 word seed phrases are secure if handled correctly, but common pitfalls—typing seeds into a compromised PC, photographing backups, or storing them in cloud services—cause most losses.
Modern alternatives:
- MPC wallets split keys across devices or servers, eliminating a single recovery phrase. Users retain usability while reducing direct exposure, but they introduce dependency on the service provider.
- Social recovery wallets delegate part of recovery to trusted contacts or entities. They simplify seed management but require trust and coordination.
Real-world scenario: A user relying on a social recovery wallet lost access temporarily when one trustee device failed during a firmware update, showing that redundancy and verification are as important as cryptography.
Multi-Signature and Layered Custody
Multisig wallets require multiple approvals to execute a transaction, making them ideal for treasuries, long-term storage, or shared custody. They reduce single-point failure risk but increase operational complexity and coordination overhead.
Examples:
- Sparrow Wallet supports multisig setups for Bitcoin, allowing distributed signatures across hardware devices.
- Multi-chain wallets rarely offer robust multisig, so advanced users often pair native wallets for cold storage with multi-chain wallets for experimentation.
Key takeaway: Multisig is overkill for modest balances but essential for managing institutional or high-value holdings.
Privacy and Transaction Anonymity
Privacy remains a major differentiator among wallets:
- Wasabi Wallet implements CoinJoin for Bitcoin, improving anonymity but limiting fee customization.
- Ethereum users must rely on zk-rollups, mixers, or privacy-centric L2s.
Advanced users combine privacy features with manual fee control to avoid leaking transaction intent. Wallets that abstract these details for convenience often hide risks, creating silent vulnerability.
Staking, NFTs, and Multi-Chain Activity
Modern wallets integrate staking, NFT management, and multi-chain swaps directly in the interface. While convenient, these features create hidden custody and approval risks:
- NFTs often involve proxy contracts or operator approvals that users fail to notice.
- Staking locks liquidity and may expose funds to slashing events if validator behavior is mismanaged.
- Multi-chain swaps can route through custodial bridges or CEX APIs, undermining the assumption of full self-custody.
Practical insight: Users should segregate experimental or staking wallets from cold storage and always review approvals, even when the UI promises “non-custodial swaps.”
Firmware and Supply Chain Security
Even hardware wallets are not immune to supply-chain risks:
- Pre-initialized devices or tampered firmware can silently compromise keys.
- Malicious update channels or dependencies, as seen in Atomic Wallet attacks (2023–2024), can drain user funds without exploiting blockchain protocols.
Mitigation strategies include firmware verification, device authenticity checks, and strict operational discipline. Cold storage reduces remote attack surface but cannot replace user vigilance.
Recommendations for 2026 Wallet Security
- Segregate wallets by purpose: cold storage for long-term assets, hot wallets for routine transactions, and experimental wallets for risky DeFi or NFT activity.
- Maintain fee control and mempool awareness: prefer wallets that allow manual fee adjustments, RBF/CPFP support, and transparent cost breakdowns.
- Enforce approval hygiene: regularly review and revoke unused token permissions; separate approval wallets from primary holdings.
- Combine authentication layers: hardware PINs, device biometrics, and software authentication reduce the attack surface.
- Leverage advanced custody judiciously: multisig, MPC, and social recovery improve resilience but require operational discipline.
- Validate supply chain: verify firmware, avoid unofficial binaries, and practice offline backup verification.
- Separate experimental activity: staking, NFTs, and multi-chain swaps should never co-reside with long-term cold storage.
Conclusion
Advanced security in 2026 is holistic, not isolated. The strongest wallets combine robust authentication, layered custody, disciplined operational practices, and clear UX. Even a technically perfect wallet cannot prevent losses if users ignore approvals, fee optimization, or recovery safeguards. The emphasis has shifted from cryptographic sophistication to system-level security, where wallet design, operational hygiene, and informed decision-making define real-world resilience.